- My goal is: I have runing Moquitto + Mongoose os + ESP32 without TLS, and now i change my yml:
tags:
-
c
sources: -
src
filesystem: -
fs
config_schema: -
[“debug.level”, 2]
-
[“mqtt.enable”, true]
-
[“mqtt.server”, “192.168.1.10:8883”]
-
[“mqtt.ssl_cert”, “ca-mongoose.crt”]
-
[“mqtt.ssl_key”, “server-mongoose.key”]
-
[“mqtt.ssl_ca_cert”, “server-mongoose.crt”]
libs: -
origin: https://github.com/mongoose-os-libs/rpc-service-config
-
origin: https://github.com/mongoose-os-libs/mjs
conds: -
when: mos.platform != “ubuntu”
apply:
sources:
libs:
- origin: https://github.com/mongoose-os-libs/wifi
- origin: https://github.com/mongoose-os-libs/ota-http-server -
when: mos.platform == “esp32”
apply:
config_schema:
build_vars:
ESP_IDF_SDKCONFIG_OPTS: >
${build_vars.ESP_IDF_SDKCONFIG_OPTS}
CONFIG_ESP32_REV_MIN_1=y -
when: mos.platform == “esp8266”
apply:
config_schema:
My init.js:
load(‘api_mqtt.js’);
load(‘api_gpio.js’);
let pin = 0, topic = ‘acaas’;
GPIO.set_button_handler(pin, GPIO.PULL_UP, GPIO.INT_EDGE_NEG, 200, function (gpio) {
print(‘Button press, GPIO’ + JSON.stringify(gpio));
if (MQTT.isConnected()) {
let res = MQTT.pub(‘acaas’, JSON.stringify({a: 1, b: 2}), 1);
print(‘Published:’, res ? ‘yes’ : ‘no’);
} else {
print(’*** MQTT is not connected ***’);
}
}, null);
this is my script to make the Self-signed:
Common parameters
SUBJ="/C=IE/ST=Dublin/L=Docks/O=MyCompany/CN=howdy"
Generate CA
openssl genrsa -out ca-mongoose.key 2048
openssl req -new -x509 -days 365 -key ca-mongoose.key -out ca-mongoose.crt -subj /C=IE/ST=Dublin/L=Docks/O=mos/CN=me
Generate client cert
openssl genrsa -out client-mongoose.key 2048
openssl req -new -key client-mongoose.key -out client-mongoose.csr -subj $SUBJ
openssl x509 -req -days 365 -in client-mongoose.csr -CA ca-mongoose.crt -CAkey ca-mongoose.key -set_serial 01 -out client-mongoose.crt
Generate server cert
openssl genrsa -out server-mongoose.key 2048
openssl req -new -key server-mongoose.key -out server-mongoose.csr -subj $SUBJ
openssl x509 -req -days 365 -in server-mongoose.csr -CA ca-mongoose.crt -CAkey ca-mongoose.key -set_serial 01 -out server-mongoose.crt
After flash ESP32 y upload 3 certificates:
mos put ca-mongoose.crt
mos put server-mongoose.crt
mos put server-mongoose.key
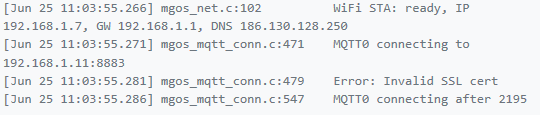
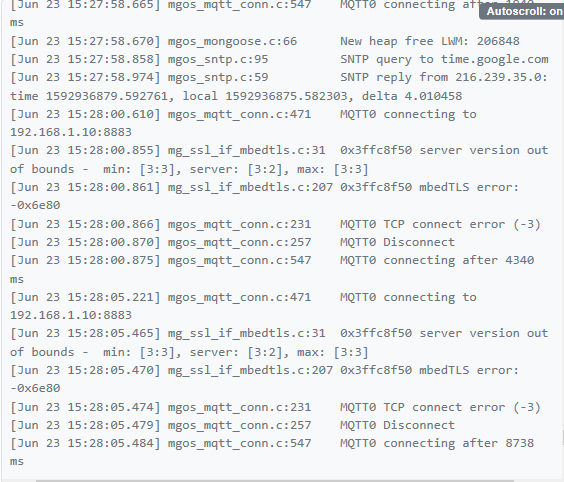
on the console I get the following error:
And my mosquitto sub:
mosquitto_sub --cafile ca.crt --tls-version tlsv1.1 --insecure -h 192.168.1.10 -t “acaas” -p 8883
I don’t now what is the problem, is the certificate? i need force use a version tlsv1.1 equal to moskitto? how is the correct path to save all certificate in my proyect?